Article
What is SOC Auditing? A Complete Guide for 2026

Mike Reeves, PhD
|
Updated on
|
Created on

Many organizations see compliance as a cost center. A System and Organization Controls (SOC) report, however, is a powerful business asset that can provide a significant competitive advantage. In a crowded market, it signals to potential customers that your company has achieved a high level of security maturity. This can shorten sales cycles, as your team can provide the report instead of completing lengthy security questionnaires. This guide explains how to use soc auditing as a strategic tool. We will explore how a clean report can differentiate your business, help you win enterprise deals, and improve your internal processes for long-term resilience.
Key Takeaways
Build customer trust with verified security: A SOC audit provides an independent evaluation from a Certified Public Accountant (CPA), confirming your organization has effective controls in place to protect client data.
Select the right audit for your business needs: A SOC 1 report focuses on controls relevant to financial reporting, while a SOC 2 report assesses operational controls based on principles like Security, Availability, and Confidentiality.
Treat compliance as a continuous process: A successful SOC program involves ongoing monitoring and internal testing, which makes annual audits smoother and helps embed security into your daily operations.
What is a SOC Audit and Why Does It Matter?
A System and Organization Controls (SOC) audit is an evaluation of how a service organization manages and protects its clients' data. For companies that handle sensitive information, a SOC audit is a critical process. It shows a commitment to maintaining high standards for data security and operational integrity. The audit is performed by an independent Certified Public Accountant (CPA).
The process results in a detailed report on the effectiveness of a company's internal controls. This report helps organizations build trust with customers and partners. It provides a clear picture of their security posture, moving the conversation from a simple promise of security to a verified statement of fact. This is especially important for technology and cloud computing vendors, where customers have limited visibility into operations.
This process is not just about meeting compliance requirements. It is a fundamental part of modern risk management. By undergoing a System and Organization Controls audit, a company demonstrates that it takes its data protection responsibilities seriously. This can be a significant factor for potential customers choosing between service providers. A favorable SOC report can shorten sales cycles and satisfy due diligence requests from enterprise clients, regulators, and business partners.
How SOC Audits Protect Data
SOC audits provide a structured framework for assessing a company's internal controls related to data security. They help businesses show they are serious about keeping information secure. The audit examines the design and operating effectiveness of these controls against established standards.
For SOC 2 and SOC 3 audits, an auditor assesses the controls against five core principles. These are known as the Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. This comprehensive evaluation ensures an organization is actively protecting sensitive information against a wide range of potential risks.
Build Trust with Independent Verification
One of the main benefits of a SOC audit is the independent verification it offers. A SOC report is an objective assessment of a service organization’s internal controls. It gives customers and stakeholders assurance that their data is being handled securely and accurately.
This third-party validation is powerful. It can improve a company's reputation and provide a competitive advantage in the marketplace. When a customer sees a clean SOC report, they have greater confidence in the provider's ability to protect their information. This reflects a strong, organization-wide commitment to security and operational excellence.
What Are the Three Types of SOC Audits?
System and Organization Controls (SOC) reports are not a one-size-fits-all solution. The American Institute of Certified Public Accountants (AICPA) has established three different types of SOC reports. Each one serves a distinct purpose, designed to meet the specific needs of different stakeholders.
Choosing the right audit depends on the services you provide and the assurances your customers require. Understanding the differences between SOC 1, SOC 2, and SOC 3 is the first step in building a strong compliance program and demonstrating trust to your clients and partners.
SOC 1: Financial Reporting Controls
A SOC 1 report focuses on a service organization’s controls that are relevant to its clients’ financial reporting. If your company provides a service that could impact a client's financial statements, this is the report you will likely need. Think of services like payroll processing, loan servicing, or data center hosting for financial applications.
These reports are intended to be used by your clients and their financial auditors. The goal is to provide assurance that your systems will not introduce errors into their financial data. The audit evaluates your control objectives and activities related to your clients’ internal control over financial reporting (ICFR).
SOC 2: Trust Services Criteria
A SOC 2 report evaluates a company’s controls over customer data. It is based on five principles known as the Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. This type of audit is essential for technology companies, SaaS platforms, and cloud computing providers that store or process sensitive information.
Unlike a SOC 1 report, a SOC 2 report is not focused on financial reporting. Instead, it provides detailed information and assurance about the controls you have in place to protect customer data. This helps your customers and partners assess the risks associated with using your services.
SOC 3: General Use Reports
A SOC 3 report is a high-level summary of a SOC 2 audit. It covers the same subject matter but is designed for a general audience and can be freely distributed. While a SOC 2 report contains sensitive details about a company’s controls and is restricted, a SOC 3 report provides a summary of the findings without the specifics.
Companies often use a SOC 3 report as a marketing tool. You can post it on your website to show potential customers that you have met the Trust Services Criteria. It offers a simplified confirmation of your compliance posture and often includes a seal from the AICPA that you can display.
Who Can Perform a SOC Audit?
A SOC audit must be performed by an independent Certified Public Accountant (CPA). This requirement is set by the American Institute of Certified Public Accountants (AICPA), the professional organization that develops and oversees SOC reporting standards. The AICPA established this rule to ensure every audit is conducted with objectivity and professional diligence.
While other consultants and advisors can help your organization prepare for an audit, they are not permitted to issue the final report. The official examination and attestation must come from a licensed CPA or a qualified public accounting firm. This separation of duties is critical for maintaining the auditor’s independence and the credibility of the final report. Choosing the right firm involves more than just verifying a CPA license; it requires finding a partner with relevant experience in your industry.
Understanding AICPA Requirements
The American Institute of Certified Public Accountants (AICPA) provides the official framework for SOC examinations. According to these standards, only a licensed CPA or an accredited CPA firm is qualified to perform a SOC audit. This requirement is fundamental to the integrity of the entire SOC reporting system.
CPAs are bound by a strict professional code of conduct that demands independence, objectivity, and ethical rigor. This ensures that an auditor’s findings are unbiased and that the resulting report is a trustworthy attestation of a company’s controls. A report issued by any individual or firm without the proper CPA credentials is not a valid SOC report. The AICPA’s guidance on attestation standards gives the final report its authority.
How to Select the Right Audit Firm
Verifying a firm’s CPA certification is the first step. The next is to evaluate its specific experience. Look for an audit firm with a strong track record of performing SOC audits for companies similar to yours in size, industry, and technology stack. An experienced auditor will understand your specific operational challenges and control environment.
When vetting potential auditors, ask about their methodology and their team's expertise with relevant systems. It is also important to distinguish between readiness consultants and auditors. While a consultant can help you identify and remediate gaps before the audit, they cannot perform the final attestation. The firm that issues your SOC report must be fully independent from your preparation activities to avoid any conflict of interest.
What Does the SOC Audit Process Involve?
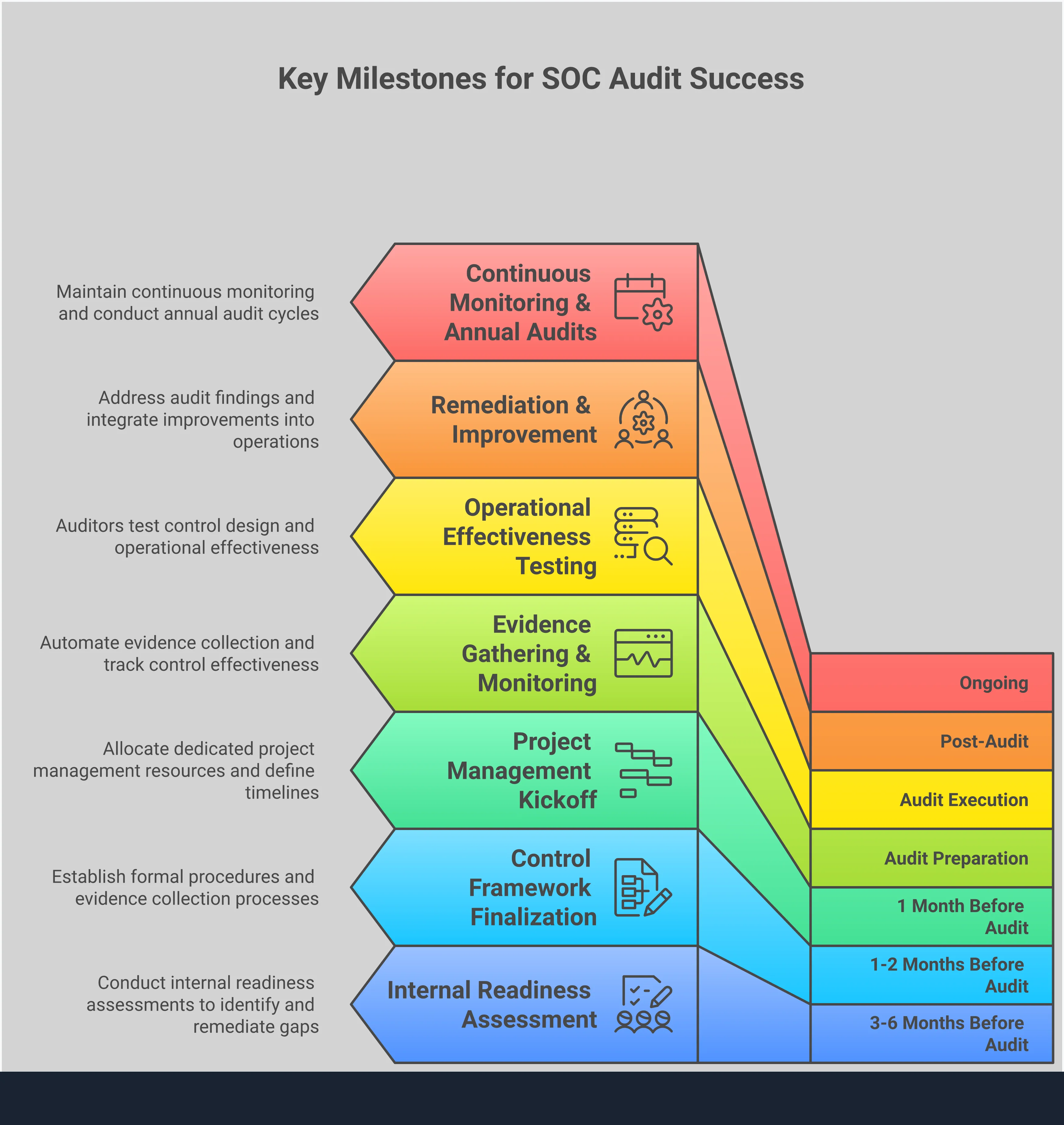
A System and Organization Controls (SOC) audit is a formal process, not a simple checklist. It follows a structured path from planning to final reporting. Each stage builds on the last, ensuring a thorough and credible review of your control environment. Understanding these steps helps you prepare your team, manage resources, and work effectively with your chosen audit firm. The process ensures that the final report is a reliable testament to your organization's security and operational integrity.
Plan and Scope the Audit
The first step is to define the audit's boundaries. You and your auditor will determine which systems, processes, and locations are included. You will also select the relevant Trust Services Criteria for your business needs. According to consulting firm CLA, a common challenge is "determining the SOC report’s scope." A poorly defined scope can lead to confusion and unnecessary work.
Getting this step right is critical. A clear plan sets expectations for everyone involved and creates a roadmap for the entire engagement. It ensures the audit focuses on the areas most important to your customers and stakeholders, preventing wasted time on out-of-scope systems.
Collect Documentation and Analyze Gaps
Next, your team gathers evidence to show your controls are in place. This includes procedures, system configurations, access logs, and employee training records. This stage often includes a gap analysis, where you compare your existing controls against the SOC 2 requirements. This helps you identify and fix weaknesses before the formal audit begins.
As noted by Tego, a data security firm, "SOC 2 can be overwhelming if your team hasn’t been through an audit before or lacks compliance expertise." A strong internal control environment is essential for success. Proactively identifying gaps gives you time to remediate issues and strengthen your position for the audit.
Execute the Audit and Test Controls
Once you have gathered your evidence, the independent auditor begins their testing. They will review your documentation, interview your team members, and perform tests to verify that your controls are working as described. The goal is to confirm that controls are both designed appropriately and operating effectively over time.
According to the compliance platform Optro, a SOC 2 audit "provides independent assurance that your organization’s controls are designed correctly and functioning over a specified period." This external validation is what gives the final report its credibility. The auditor’s objective testing provides customers with confidence in your systems.
Generate and Deliver the Report
The final stage is the creation of the SOC report. The auditor compiles their findings, including a description of your system, the controls tested, and the results of those tests. This formal document is the deliverable you can share with customers and partners.
This report serves as proof of your commitment to security and compliance. As consulting firm IS Partners explains, SOC reports help organizations "reduce repetitive security questionnaires and demonstrate security maturity." The report becomes a valuable tool for building trust and satisfying due diligence requests, saving your team significant time and effort in the long run.
What Are the Trust Services Criteria?
The Trust Services Criteria are a set of standards used to evaluate and report on an organization's controls over its information and systems. Developed by the American Institute of Certified Public Accountants (AICPA), these criteria provide the framework for a SOC 2 audit. They help auditors assess how well a service organization protects its clients' data based on five distinct categories.
While every SOC 2 audit must include the Security criterion, the other four are optional. A company will select the additional criteria that are most relevant to the services it provides and the commitments it makes to its customers. This allows the SOC 2 report to be tailored to the specific nature of the business. Understanding these five categories is the first step in preparing for a successful audit.
The five categories are:
Security: Protecting information and systems.
Availability: Ensuring systems are accessible as agreed.
Processing Integrity: Verifying that system processing is accurate and authorized.
Confidentiality: Protecting sensitive information from unauthorized disclosure.
Privacy: Handling personal information according to privacy commitments.
Security
The Security criterion is the foundation of any SOC 2 report and is mandatory for all audits. It is often called the "common criteria" because its controls overlap with and support the other four categories. This principle focuses on the protection of information and systems against unauthorized access, unauthorized disclosure of information, and damage to systems.
To meet this criterion, an organization must demonstrate it has effective controls in place. These often include network firewalls, intrusion detection systems, and multi-factor authentication. The goal is to show that the system is protected, both logically and physically, from security events that could compromise the other Trust Services Criteria.
Availability
The Availability criterion addresses the accessibility of a system, product, or service. It focuses on whether the system is available for operation and use as committed or agreed upon. This is especially important for companies that provide services their customers rely on for their own business operations, such as cloud hosting or software-as-a-service (SaaS) platforms.
Controls related to availability often involve performance monitoring, disaster recovery planning, and incident response procedures. An auditor will evaluate whether the organization has taken sufficient steps to minimize downtime and ensure it can meet its service level agreements (SLAs). This provides assurance to customers that the service will be there when they need it.
Processing Integrity
The Processing Integrity criterion evaluates if a system processes data in a reliable and timely manner. It addresses whether system processing is complete, valid, accurate, and authorized. The goal is to ensure that the system achieves its purpose without errors, delays, or unauthorized manipulation.
This criterion is relevant for organizations that perform transaction processing or critical data calculations for their clients. For example, a financial services platform would need strong processing integrity controls to ensure that all transactions are handled correctly. An audit would examine the quality assurance procedures and data monitoring controls to verify that system inputs and outputs are consistently accurate.
Confidentiality
The Confidentiality criterion focuses on protecting information that is designated as confidential. This principle ensures that sensitive data is protected from unauthorized disclosure. Confidential information can include business plans, intellectual property, financial reports, or any other data that is restricted to a specific set of people or organizations.
To meet this criterion, a company must implement robust controls like data encryption, access control lists, and confidentiality agreements with employees and partners. Unlike the Privacy criterion, which applies specifically to personal information, Confidentiality covers a broader range of sensitive business data. It demonstrates a commitment to safeguarding proprietary information throughout its lifecycle.
Privacy
The Privacy criterion is distinct from Confidentiality and applies specifically to personal information. It addresses how an organization collects, uses, retains, discloses, and disposes of personally identifiable information (PII). This criterion aligns with the organization's privacy notice and with criteria set forth in generally accepted privacy principles.
Controls for privacy include providing clear notice to individuals about data practices, obtaining consent for data collection, and honoring user requests for data access or deletion. An audit against the Privacy criterion gives customers and partners confidence that their personal data is handled responsibly and in accordance with stated policies and applicable privacy regulations.
How Can You Prepare for a SOC 2 Audit?
Preparing for a System and Organization Controls (SOC) 2 audit is a structured process. It requires careful planning and internal alignment long before the auditor arrives. By taking a few key steps, you can streamline the audit, reduce stress on your team, and improve your chances of a successful outcome. The process generally involves defining your internal rules, gathering proof that you follow them, and testing everything yourself first.
Establish a Control Framework
Your control framework is the foundation of your SOC 2 compliance. It is a formal set of procedures and controls that documents how your organization meets the Trust Services Criteria. According to the security firm Tego, "Without a strong internal control environment, your organization may fail to meet SOC 2’s Trust Services Criteria."
This framework acts as your rulebook for protecting customer data. It should clearly define responsibilities and outline the specific actions your team takes to maintain security, availability, and confidentiality. A well-defined framework provides a clear roadmap for both your team and the auditor, showing how your daily operations align with your compliance goals.
Manage Evidence and Documentation
A SOC 2 audit requires you to prove your controls are operating effectively. This means collecting and organizing evidence for the auditor to review. Evidence can include system configuration screenshots, access logs, employee training records, and signed procedure documents. It’s a detailed process that goes beyond technical settings.
As the compliance platform TrustCloud notes, "SOC 2 isn’t just about servers, logs, or access controls; it’s about how people work, make decisions, and interact with security in their day-to-day roles." Manually gathering this documentation is a significant challenge. Using a governance intelligence platform can help automate evidence collection and ensure everything is organized and ready for inspection.
Test Internally and Remediate Findings
Before the official audit begins, you should conduct an internal readiness assessment. This is like a practice audit where you test your own controls against the SOC 2 criteria. This step helps you identify any gaps or weaknesses in your security posture ahead of time, giving you a chance to fix them.
Many organizations struggle when they don't fully understand the requirements. The advisory firm CLA states that service organizations "may need to invest time and resources into strengthening internal controls before they can issue a SOC report." An internal review helps you find these areas for improvement. Addressing issues proactively makes the formal audit process much smoother and reduces the risk of negative findings in your final report.
What Are Common SOC Audit Challenges?
A SOC audit provides valuable assurance to your customers, but the process can be demanding. Many organizations encounter similar hurdles, especially during their first audit cycle. These challenges often fall into three main areas: defining the project's boundaries, allocating the necessary people and time, and managing the organizational changes required for compliance.
Understanding these common obstacles is the first step to creating a smoother audit experience. With careful planning, you can anticipate these issues and develop a strategy to address them before they delay your report. Preparing for these challenges helps your team stay focused on the goal: demonstrating a strong control environment to build and maintain customer trust. The journey to a successful SOC report involves more than just technical checks; it requires careful coordination across your entire organization. From the initial scoping discussions to the final report delivery, each phase presents unique difficulties that can derail progress if not managed properly. By recognizing these potential roadblocks early, you can allocate resources more effectively and set realistic expectations for stakeholders. This proactive approach not only streamlines the audit but also strengthens your internal control environment for the long term.
Defining Scope and Requirements
One of the first and most critical challenges is defining the audit's scope. Many organizations, particularly those new to the process, struggle to understand the requirements and determine which systems and services to include. The scope defines the boundaries of the audit. It clarifies which of the five Trust Services Criteria apply and which business operations are being evaluated.
If the scope is too narrow, the final report may not cover the services your customers care about, reducing its value. If it’s too broad, you create unnecessary work by including irrelevant systems and controls. Getting the scope right requires a clear understanding of your service commitments and customer expectations from the very beginning.
Managing Resources and Timelines
A SOC audit is a significant project that demands time and attention from multiple departments, not just your compliance team. Achieving compliance can feel overwhelming for teams without prior audit experience. The process requires input from engineering, human resources, and operations to gather evidence and implement or refine controls. This work comes on top of everyone's existing day-to-day responsibilities.
Without a dedicated project manager and clear timelines, the audit can easily fall behind schedule. Successful audits depend on effective project management to coordinate tasks, track progress, and ensure everyone understands their role. Allocating sufficient resources and setting realistic deadlines are essential for keeping the audit on track.
Overcoming Internal Resistance
Compliance is not just about technology; it’s about people and processes. A SOC 2 audit often requires changes to how people work, make decisions, and handle data in their daily roles. Implementing new security controls or documentation procedures can be met with resistance from employees who view them as inconvenient or disruptive.
This resistance is a common but often unexpected challenge. To overcome it, you need to communicate the business reasons behind the changes. When employees understand that these new processes protect the company and its customers, they are more likely to adopt them. Building a culture of security where everyone feels a sense of shared responsibility is key to long-term compliance success.
What Misconceptions Can Hinder a SOC Audit?
Misunderstandings about the System and Organization Controls (SOC) audit process can create significant roadblocks. They often lead to poor planning, wasted resources, and even failed audits. Addressing these common myths helps your team prepare effectively and approach the audit with clarity. By understanding what a SOC audit truly entails, you can set realistic expectations and build a sustainable compliance program that supports your business goals.
Misconception 1: SOC Is a One-Time Project
Many teams view a SOC audit as a single project with a clear finish line. This is a common mistake. Achieving compliance is not a one-time event; it is an ongoing commitment. As the firm Johanson LLP notes, "maintaining compliance requires continuous monitoring and regular audits." A SOC 2 Type I report only examines your controls at a single point in time. A Type II report, which most customers expect, evaluates how well those controls operate over a period, usually six to twelve months. This requires a continuous effort to manage evidence, monitor performance, and address any gaps that arise.
Misconception 2: All SOC Reports Are the Same
Another frequent error is assuming all SOC reports provide the same level of assurance. In reality, they can vary widely. The scope of a SOC 2 audit depends on which of the five Trust Services Criteria are included: Security, Availability, Processing Integrity, Confidentiality, and Privacy. A report covering only Security offers a much different picture than one that includes all five. Furthermore, the difference between a Type I and Type II report is significant. Believing all reports are equal can lead you to accept a vendor's report that doesn't actually meet your organization's risk requirements.
Misconception 3: A SOC Audit Is Just a Checklist
It's easy to think of a SOC audit as a simple checklist to complete. This view misses the entire point of the framework. A SOC audit is not about just having policies in place. It is a deep evaluation of whether your organization's systems and processes actually work as described. According to the advisory firm Sikich, SOC 2 is a framework that evaluates whether an organization meets its service commitments. Auditors test the operating effectiveness of your controls, which requires you to provide clear evidence of them in action. Simply having a written policy is not enough; you must demonstrate that it is consistently followed.
How Often Should You Get a SOC Audit?
Most organizations get a SOC audit annually. This yearly cycle assures customers and partners that your controls remain effective as your business evolves. While an annual report is standard, your specific needs might differ. Customer contracts or industry norms can require more frequent audits.
The first audit is usually the most demanding. After that, the process becomes smoother if you maintain your controls throughout the year. The goal is to shift from a one-time compliance event to a state of continuous readiness. This approach makes each audit cycle easier and reduces the risk of finding unexpected control failures.
Type I vs. Type II Reports
A key decision in the SOC audit process is choosing between a Type I and a Type II report. A Type I report evaluates the design of your security controls at a single point in time. It confirms that your controls are designed properly to meet their objectives. This type of report is often faster to complete.
A Type II report provides a deeper analysis. It examines both the design and the operational effectiveness of your controls over a period, usually three to 12 months. This report shows that your controls have worked as intended over time, offering greater assurance to your customers. Understanding the full SOC audit process helps you choose the right report for your business.
The Role of Continuous Monitoring
Maintaining SOC compliance is not just about passing an annual audit. It requires integrating security practices into your daily operations. This shift toward continuous monitoring helps organizations build a resilient framework where compliance becomes part of the company culture.
As one report on SOC 2 challenges notes, compliance is about "how people work, make decisions, and interact with security in their day-to-day roles." Instead of scrambling to prepare for an audit, continuous monitoring ensures you are always ready. This approach involves regularly testing controls, managing evidence, and addressing gaps as they arise. It transforms compliance from a periodic burden into a strategic advantage.
What Are the Benefits of a SOC Report?
A System and Organization Controls (SOC) report is more than a compliance document. It is a valuable asset that can strengthen your business from the inside out. Pursuing a SOC audit helps formalize security practices, build trust with clients, and create a clear advantage in the market. The benefits extend beyond passing the audit itself.
Increase Customer Confidence
A SOC report provides independent validation that your organization protects customer data. This is critical for building trust, especially when handling sensitive information. For many enterprise customers, a SOC 2 report is a mandatory part of their vendor security review process. Presenting a clean report from a certified public accountant (CPA) firm shows a serious commitment to security. It answers many of your customers' security questions before they even ask them. This makes them more confident in choosing your services and helps streamline procurement conversations.
Gain a Competitive Advantage
In a crowded market, a SOC report can be a key differentiator. It signals to potential customers that your organization has achieved a higher level of security maturity. This can shorten sales cycles, as your team can provide the report instead of filling out lengthy, custom security questionnaires. An "unqualified opinion" in your report, meaning the auditor found no material issues, gives you a strong competitive edge. It demonstrates that your controls are designed and operating effectively, setting you apart from competitors who may lack the same level of audited assurance.
Improve Internal Processes
The process of preparing for a SOC audit forces you to examine and document your internal controls. This exercise often uncovers inefficiencies or gaps in your security and operational procedures. Addressing these findings leads to stronger, more consistent processes across the organization. It helps embed security into your company culture, rather than treating it as an afterthought. This internal discipline not only prepares you for the audit but also improves your overall risk management and operational resilience long-term.
Related Articles
SOC Auditing FAQs
Table of Contents

Mike Reeves, PhD
Mike is a key figure at the intersection of psychology and technology. He has created and managed algorithms and decision-making tools used by more than half of the Fortune 100.
