Article
The IT Audit Process: How It Works & Why It Matters

Mike Reeves, PhD
|
Updated on
|
Created on

An information technology (IT) audit often feels like a necessary disruption. It pulls key staff away from their daily work for weeks, sometimes months. Teams scramble to gather documents, answer questions, and prepare systems for review. This process consumes valuable time and resources, creating friction across the organization. But it does not have to be this way. A well-structured IT audit can be more than just a compliance check; it can be an efficient process that strengthens security and improves operations. This guide explains how the audit process works, what it covers, and how you can prepare your team for a smoother, more valuable assessment.
Key Takeaways
Understand the purpose of an IT audit: It is a formal review of technology systems and controls designed to manage risk, verify regulatory compliance, and improve operational efficiency.
Prepare proactively to ensure a smooth audit: A successful process depends on organizing documentation, coordinating with stakeholders, and performing internal reviews before the audit begins.
Use audit findings to drive continuous improvement: The final report is a tool for building a sustainable program that addresses control gaps and maintains a constant state of readiness.
What Is an IT Audit?
An information technology (IT) audit examines an organization's technology infrastructure, applications, and operations. The process helps confirm that IT controls protect company assets and data. It also ensures that IT systems operate effectively and align with overall business goals. The scope of an IT audit can vary, but the core purpose remains consistent: to evaluate and improve technology governance and management.
Defining the IT Audit and Its Purpose
An IT audit is a formal review of a company's technology systems, processes, and controls. According to the tech resource JumpCloud, it's like a "health check-up for a company's technology systems." The goal is to verify that technology is secure, efficient, and compliant with relevant standards.
The purpose extends beyond just finding problems. A thorough IT audit process confirms that technology helps the business achieve its objectives. Auditors assess risks, review security measures, and check for compliance with internal rules and external regulations. This evaluation provides assurance to leadership that the organization's technology is managed properly and supports its strategic direction.
Common Types of IT Audits
IT audits can be categorized based on their specific objectives. While there are many specialized reviews, most fall into a few common types. Understanding these categories helps organizations focus their efforts on the areas that matter most to their business and risk profile.
A security audit is one of the most frequent types. It looks for vulnerabilities in data protection, such as weak access controls or firewall configurations. A compliance audit checks if IT systems adhere to specific regulations, like the Health Insurance Portability and Accountability Act (HIPAA) or SOC 2 criteria. Finally, an operational audit evaluates the efficiency and effectiveness of IT processes to ensure they support business operations without waste.
Why Are IT Audits Important?
An information technology (IT) audit is a core part of modern business management. It provides an independent evaluation of your technology systems, controls, and processes. This assessment helps confirm that your IT infrastructure supports your organization's goals effectively while managing critical risks. Regular IT audits are essential for protecting assets, meeting legal obligations, and improving overall performance.
Manage Security and Risk
IT audits identify vulnerabilities in your technology systems before they can be exploited. This proactive approach protects sensitive data and ensures your IT infrastructure remains stable and reliable. As businesses adopt more complex technologies, the risk of new cybersecurity threats also grows. An audit provides a clear picture of these risks, allowing you to address them before they cause significant financial or reputational damage. It is a fundamental part of a strong security posture, helping you find and fix issues before they become expensive problems.
Meet Regulatory Requirements
Many industries operate under strict rules for data privacy and security. An information technology audit verifies that your company follows these requirements, such as those found in HIPAA for healthcare or SOC 2 for service organizations. The process ensures your technology assets are secure and managed according to established best practices. Demonstrating this regulatory compliance is essential for avoiding penalties, maintaining certifications, and building trust with customers and partners. An audit report serves as formal evidence that your controls are effective and meet industry standards.
Improve Operational Performance
Beyond security and compliance, IT audits can make your business run better. The process often uncovers slow or inefficient IT processes that create bottlenecks for your teams. By identifying these weak spots, you can make targeted improvements that save time and resources. The findings from an audit also provide valuable data to guide technology investments. Instead of guessing where to allocate your budget, you can make informed decisions based on a clear assessment of your systems' performance and needs, ensuring you spend money where it will have the greatest impact.
What Does an IT Audit Cover?
An information technology (IT) audit examines several key areas to confirm that systems are secure, reliable, and compliant. Auditors look at everything from system security and network infrastructure to data management and internal documentation. Each component provides a piece of the overall picture of an organization's IT health.
Assess System Security
Auditors assess system security to confirm data and systems are safe. This review checks for vulnerabilities that could lead to unauthorized access or data breaches. The audit team examines security measures like firewalls, antivirus software, and user access controls. They verify that only authorized personnel can access sensitive information. According to security provider JumpCloud, this step is fundamental to confirming that an organization's digital assets are properly protected against threats.
Review Infrastructure and Networks
An IT audit also reviews a company's infrastructure and networks. This covers all physical and virtual hardware supporting business operations, like servers, routers, and cloud environments. Auditors evaluate whether the infrastructure is stable and efficient. As noted by IT service management firm InvGate, the goal is to ensure technology works well and helps the business. The review confirms that network configurations are secure and systems are maintained properly to prevent downtime.
Evaluate Data Management and Privacy
An audit evaluates how an organization manages its data to protect sensitive information. Auditors check data protection practices for compliance with regulations like the Health Insurance Portability and Accountability Act (HIPAA). They look at how data is stored, encrypted, and backed up. The review also covers data retention and disposal procedures. This part of the audit verifies that the company follows established data privacy principles and protects information throughout its lifecycle.
Analyze Documentation and Controls
Finally, auditors analyze documentation and internal controls by reviewing written procedures and system records. The goal is to confirm that the organization's rules are followed consistently. Auditors need clear evidence that controls are working as designed. According to compliance experts at MSECB, process owners must be able to find and share information quickly. Well-organized documentation demonstrates a formal approach to managing the IT environment and makes the audit process more efficient.
How Does the IT Audit Process Work?
An information technology (IT) audit follows a structured, four-stage process. It begins with careful planning and ends with a clear path for improvement. Each stage builds on the last, creating a comprehensive review of an organization’s IT environment. This methodical approach ensures that auditors can systematically evaluate systems, identify risks, and verify that controls are working as intended. The goal is to provide leadership with a reliable assessment of their technology governance and security posture. Understanding these four stages helps organizations prepare for the audit, collaborate effectively with auditors, and make the most of the final report.
Define the Plan and Scope
The first stage is creating a detailed audit plan. Auditors work with management to define the scope, which clarifies which systems, applications, and processes will be reviewed. This includes setting clear objectives and timelines. The scope must account for current business operations and emerging technologies. According to The Ohio Society of CPAs, organizations need auditors to help them align with regulatory changes and audit new technologies like artificial intelligence (AI) and blockchain. A well-defined scope prevents misunderstandings and keeps the audit focused on the most critical areas, ensuring the process is efficient and relevant to the organization’s goals.
Assess Risk and Business Impact
Next, auditors conduct a risk assessment to identify potential threats to the organization’s IT systems. This step helps prioritize the audit work by focusing on areas with the highest risk and potential business impact. Auditors evaluate the likelihood and consequences of various threats, such as data breaches, system failures, or non-compliance. This analysis guides the audit tests that will be performed later. Managing the scope is critical here. As noted by MSECB, clear communication between auditors and the organization is necessary to maintain focus on key objectives and avoid scope creep, where the audit expands beyond its original plan.
Collect and Test Evidence
This stage involves the hands-on work of gathering and evaluating evidence. Auditors collect documentation like system logs, access reports, and procedural documents to test whether controls are designed correctly and operating effectively. They may also interview staff and observe processes directly. This can be a time-consuming part of the audit. However, as the compliance firm A-LIGN points out, organizations can streamline evidence collection by using governance, risk management, and compliance (GRC) technology. Automation helps centralize evidence and reduce the manual effort required from both auditors and internal teams, leading to a smoother and faster audit cycle.
Report Findings and Plan Remediation
In the final stage, auditors compile their findings into a formal report. This document summarizes the audit’s scope, objectives, and results. It details any identified weaknesses, control gaps, or compliance issues, often categorizing them by severity. The report also includes recommendations for corrective action. Clear communication is essential for making these findings useful. The report is not just a critique; it is a tool for improvement. It serves as the foundation for creating a remediation plan, where the organization outlines the specific steps it will take to address the findings and strengthen its IT controls.
Common Challenges in IT Audits
IT audits are essential for maintaining security and compliance, but they are rarely simple. The process often presents significant hurdles that can strain resources and create friction between teams. From keeping up with new technologies to navigating a web of regulations, organizations face several recurring obstacles. Understanding these common challenges is the first step toward developing a more efficient and effective audit strategy. By anticipating these issues, your team can prepare proactive solutions instead of reacting to problems as they arise.
Managing Limited Resources
One of the biggest hurdles in any IT audit is the strain it places on internal resources. Compliance teams often operate with tight budgets and limited staff, making audit preparation a demanding task. According to a report from A-LIGN, two-thirds of organizations spend at least three months each year preparing for every single audit. This significant investment of time and money pulls key personnel away from their primary duties, impacting productivity across the business. When your most skilled people are tied up gathering evidence and answering auditor questions, their strategic work gets put on hold.
Addressing New Technology and Cyber Risks
Technology is evolving faster than ever, and audit practices are struggling to keep pace. Organizations are adopting new tools like artificial intelligence and blockchain to innovate, but these systems also introduce new vulnerabilities. Auditors must now assess complex, automated environments where traditional testing methods may not apply. According to The Ohio Society of CPAs, a key challenge is auditing novel technologies while also securing the business against emerging threats. This creates a difficult balancing act, requiring specialized skills and new approaches to validate that controls are designed and operating effectively.
Handling Complex Regulations
The regulatory environment is not static. New standards emerge and existing ones are updated, forcing organizations to constantly adapt their compliance programs. Managing these complex and often overlapping requirements is a major challenge for audit teams. Another common issue is scope creep, where an audit expands beyond its initial objectives. This can happen when initial findings lead to more questions, pulling in additional systems or processes. As noted by MSECB, managing scope creep requires clear alignment between auditors and the business to keep the audit focused and efficient, preventing unnecessary delays and costs.
Closing Communication Gaps
A successful audit depends on clear and consistent communication. Misunderstandings between auditors and internal teams can lead to delays, repeated requests for information, and incorrect findings. A common point of failure is when process owners cannot quickly locate or explain the evidence auditors need. This is especially true if they are not familiar with the organization's document management system. To prevent this, it is crucial to establish clear lines of communication and ensure that everyone involved understands their role and has access to the necessary information before the audit begins.
How to Prepare for an IT Audit
A successful information technology (IT) audit begins long before the auditors arrive. Preparation is the most critical factor in ensuring a smooth and efficient process. When you approach an audit proactively, you can minimize disruptions to your daily operations and reduce the stress on your team. It also demonstrates to auditors that your organization has a mature and organized approach to governance and compliance.
A well-planned preparation strategy allows you to identify and address potential issues on your own terms. Instead of reacting to findings, you can present a clear and accurate picture of your control environment. This builds confidence with auditors and stakeholders, showing that you are in command of your security and compliance posture.
Think of audit preparation as an opportunity to validate your internal processes and find areas for improvement. It helps align your team, clarify responsibilities, and reinforce the importance of your compliance program. By taking the time to get organized, you can turn a potentially challenging assessment into a valuable business exercise. The following steps provide a clear roadmap for getting your team and systems ready for an audit.
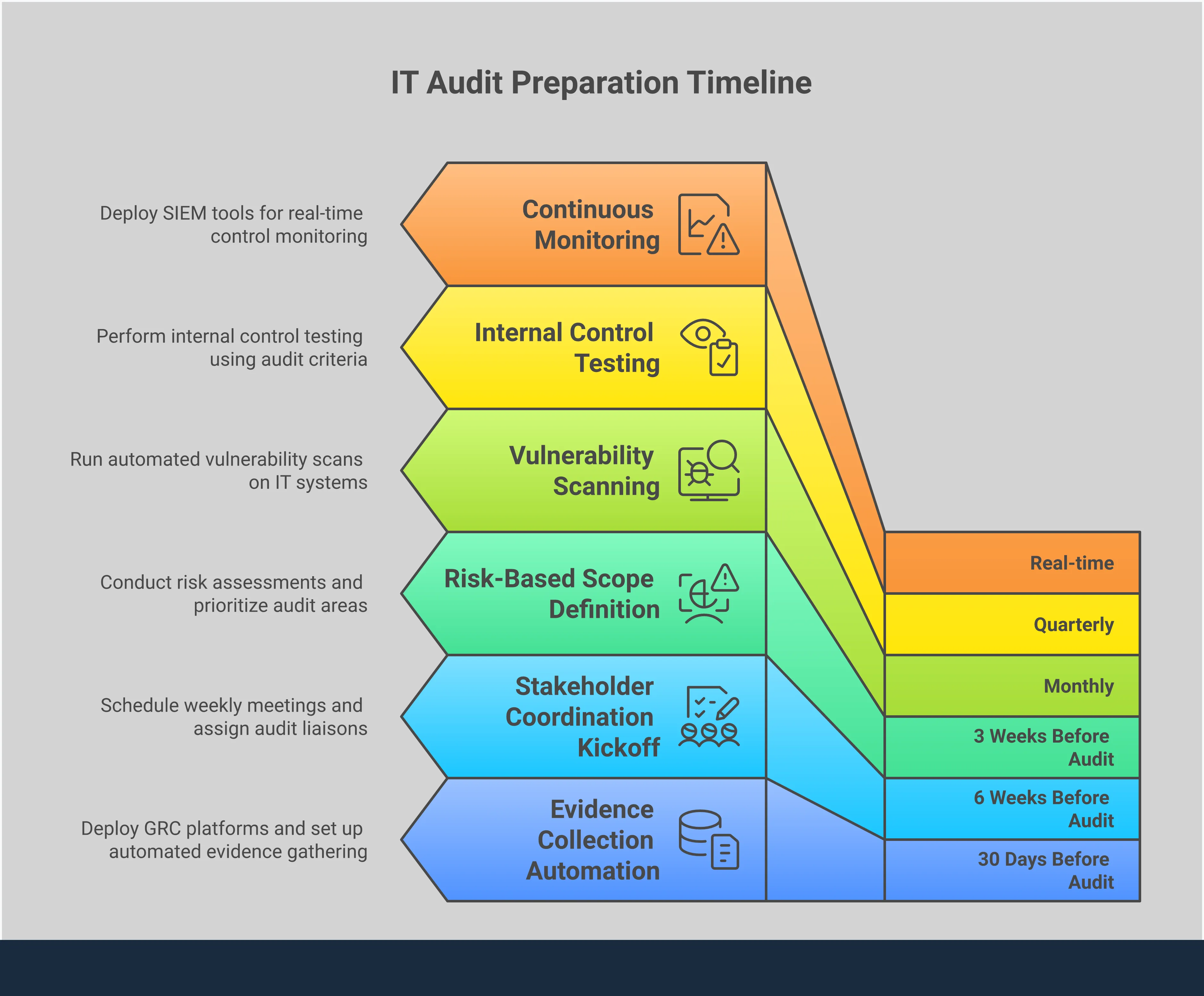
Gather Documentation and Evidence
Your first step is to collect and organize all relevant documentation. This includes procedures, network diagrams, system configurations, access control lists, and previous audit reports. Having this information readily available saves time and shows the auditor that your controls are well-managed. Centralizing your documents in one place prevents a last-minute scramble for evidence.
According to the audit firm A-LIGN, organizations can streamline evidence collection by using governance, risk management, and compliance (GRC) technology. These platforms help automate the gathering of logs and other evidence, ensuring everything is complete and easy to access. This preparation makes the audit process less disruptive for everyone involved.
Coordinate System Access and Stakeholders
An audit requires collaboration between your team and the auditors. You need to coordinate schedules and ensure key personnel are available for interviews. It is also important to arrange for auditors to have the appropriate, read-only access to the systems they need to review.
Clear communication is essential. As the certification body MSECB notes, it is "crucial that process owners or other relevant individuals... are familiar with their document management system and how to quickly and accurately get information." Make sure your team members understand the audit's scope and are prepared to explain their roles and responsibilities. This coordination helps prevent delays and ensures auditors get the information they need without confusion.
Conduct Internal Pre-Audit Reviews
A pre-audit review is like a dress rehearsal for the main event. Conducting an internal assessment helps you identify and remediate gaps before the external auditors find them. This self-assessment should follow the same scope and criteria as the official IT audit. This allows you to test your controls and documentation in a low-pressure environment.
This proactive step is especially important as technology and regulations change. The Ohio Society of CPAs highlights that organizations need more from their audit departments to ensure change initiatives align with compliance. An internal review confirms you are keeping up with new requirements and gives your team valuable practice for the formal audit.
Confirm Technology and Process Readiness
Your documentation might say one thing, but your technology and processes must reflect it. Before the audit, verify that your controls are implemented correctly and operating as intended. This includes testing security configurations, reviewing user access permissions, and confirming that data backup and recovery procedures work.
As new risks emerge, IT auditors play a key role in helping organizations navigate threats. Confirming your readiness shows that your compliance program is more than just a paper exercise. It proves that your controls are effective in protecting your systems and data, which is the ultimate goal of any IT audit.
Key IT Audit Standards and Frameworks
IT audits are not conducted in a vacuum. They rely on established standards and frameworks to provide structure, consistency, and clear benchmarks for evaluation. These frameworks help organizations manage risk and demonstrate compliance to stakeholders.
Understanding the most common ones can help you prepare for an audit and build a stronger security and governance program. Each framework serves a different purpose, from information security to overall IT governance.
ISO 27001 for Information Security
ISO/IEC 27001 is a global standard for creating an Information Security Management System (ISMS). An ISMS is a systematic approach to managing sensitive company information so that it remains secure. It applies to all forms of data, including digital, paper-based, and cloud-based information.
The standard requires organizations to identify information security risks through a formal assessment process. Based on that assessment, you must select and implement security controls to reduce risks to an acceptable level. The framework also requires continuous monitoring and improvement of the Information Security Management System. Achieving certification demonstrates a clear commitment to protecting information assets.
SOC 2 Trust Services Criteria
A SOC 2 report is designed for service organizations that store customer data in the cloud. The audit focuses on a company’s internal controls as they relate to the Trust Services Criteria developed by the American Institute of Certified Public Accountants (AICPA).
These five criteria are Security, Availability, Processing Integrity, Confidentiality, and Privacy. An organization can choose to be evaluated on any or all of them. A successful SOC 2 audit shows that a company has effective controls in place to manage and protect customer data. This is especially important for technology companies and cloud service providers.
NIST Cybersecurity Framework
The NIST Cybersecurity Framework offers guidance for organizations to manage and reduce cybersecurity risk. Developed by the U.S. National Institute of Standards and Technology (NIST), it is a voluntary framework that is widely adopted in the private sector.
It organizes cybersecurity activities into five core functions: Identify, Protect, Detect, Respond, and Recover. This structure helps organizations understand their security posture and create a plan for improvement. The framework is designed to be flexible, allowing companies of any size to adapt it to their specific needs. It provides a common language for discussing cybersecurity risk across an organization.
COBIT for IT Governance
COBIT, which stands for Control Objectives for Information and Related Technologies, is a framework for the governance and management of enterprise IT. It provides a comprehensive set of practices and tools to connect IT goals with broader business objectives.
The framework helps ensure that IT investments create value and that technology-related risks are properly managed. COBIT provides a structured approach to organizing and implementing IT governance and management practices. By using COBIT, organizations can build a more effective governance structure that supports their overall strategy and goals, ensuring that IT functions as a strategic partner to the business.
How to Streamline Your IT Audit
An efficient audit process saves time, reduces business disruption, and produces more reliable findings. Instead of treating an information technology audit as a disruptive annual event, you can implement practices that make it a smoother, more valuable exercise. These strategies help your team stay prepared and turn audit insights into real operational improvements.
Adopt a Risk-Based Approach
A risk-based approach focuses your audit efforts on the areas that pose the greatest threat to your organization. This means prioritizing systems, processes, and data that are most critical to your business objectives. As new technologies emerge, auditors must help organizations manage change initiatives and the novel risks they introduce. By concentrating on high-risk areas, you can allocate your limited resources more effectively. This ensures that the most significant vulnerabilities are identified and addressed, rather than spending equal time on low-impact controls.
Use Technology and Automation
Manual evidence collection is time-consuming and can lead to inconsistent results. Using technology can automate repetitive audit tasks and improve accuracy. Governance, risk management, and compliance (GRC) platforms help streamline evidence collection, saving both time and resources. Automation tools can connect to various business systems to pull data, test controls, and flag exceptions in real time. This frees up your audit and compliance teams to focus on analyzing results and providing strategic advice, rather than getting stuck on administrative work.
Establish Continuous Monitoring
An audit should be more than a point-in-time assessment. Continuous monitoring shifts your program from a periodic review to an ongoing process. This approach provides a real-time view of your control environment, helping you identify and remediate issues as they occur. With cyber threats becoming more sophisticated, a continuous approach is essential for managing risk. According to a recent survey, many organizations expect next-gen cyber threats to be their most significant challenge. Continuous monitoring helps you stay prepared and maintain compliance between official audit cycles.
Communicate Clearly with Stakeholders
Effective communication is the foundation of a successful audit. Misunderstandings between auditors, IT teams, and business leaders can cause significant delays and frustration. It is crucial that everyone involved understands the audit's scope, objectives, and timeline. Process owners should be prepared to provide information quickly and accurately. Establishing clear communication channels, holding regular check-in meetings, and documenting requests and responses can prevent confusion. When everyone is aligned, the audit process becomes a collaborative effort rather than an adversarial one.
How to Address IT Audit Findings
Receiving an IT audit report is not the end of the process. It is the beginning of the improvement cycle. The findings, whether minor recommendations or significant concerns, provide a clear roadmap for strengthening your organization’s security, governance, and operational effectiveness. A structured approach to addressing these findings ensures that you not only fix the immediate issues but also build a more resilient compliance posture for the future.
The goal is to move from a reactive cycle of fixing problems to a proactive state of continuous readiness. This involves a methodical process of analyzing the report, creating a detailed action plan, and verifying that the solutions are working as intended. By treating the audit report as a strategic tool, your team can turn findings into opportunities for meaningful improvement. This approach helps manage risk, meet regulatory requirements, and improve overall performance across the business.
Analyze and Prioritize the Report
Once you receive the audit report, the first step is to thoroughly review and understand each finding. Avoid adopting a reactive approach, which often leads to inefficiencies and disorganization during remediation. Instead, work with your team to categorize each item based on its associated risk level. Findings are typically classified as critical, high, medium, or low risk.
This prioritization helps you allocate resources effectively, focusing first on the most significant vulnerabilities that could impact the organization. Discuss the root cause of each finding with the relevant stakeholders. Was it a technology gap, a process failure, or a lack of training? Understanding the "why" behind each issue is essential for developing effective and lasting corrective actions.
Plan and Implement Corrective Actions
With a prioritized list of findings, the next step is to create a formal corrective action plan. For each finding, document the specific remediation tasks, assign a clear owner responsible for completion, and set a realistic deadline. This plan creates accountability and provides a clear path forward for everyone involved.
Effective remediation depends on clear communication and collaboration between departments. Process owners must have access to their document management system and understand how to provide evidence that a control has been fixed. Track the progress of each action item regularly. This ensures that remediation stays on schedule and allows you to address any roadblocks as they arise.
Follow Up and Verify Results
Implementing a fix is not the final step. You must also verify that the corrective action has resolved the underlying issue and is sustainable over time. This involves testing the new controls to confirm they are working correctly. You can do this through internal reviews or by having the internal audit team re-validate the fix.
This follow-up process is also an opportunity to update documentation and procedures to reflect the changes. As regulations and technology evolve, organizations need to ensure their compliance programs keep pace. Staying current with requirements for auditing novel technologies like artificial intelligence is critical for long-term success. This verification step closes the loop on the audit finding and prepares you for future audits.
Build a Sustainable IT Audit Program
An effective information technology audit program is not a series of isolated events. It is a continuous cycle designed to support long-term business goals. Building a sustainable program helps you move from reactive compliance checks to proactive risk management.
This approach reduces the burden on your teams, improves security posture over time, and ensures you are always prepared for the next assessment. A sustainable program is built on a predictable schedule, the right mix of resources, and a commitment to continuous improvement.
Set an Audit Schedule
Many organizations fall into a reactive audit cycle. According to research from A-LIGN, two-thirds of companies spend at least three months preparing for each audit. This constant state of preparation creates common challenges that consume significant time and resources.
A formal audit schedule transforms this process. By planning audits in advance, you can allocate resources effectively and integrate evidence collection into daily workflows. This proactive approach minimizes disruption and reduces the stress associated with last-minute preparations. It turns the audit into a manageable, routine activity instead of an annual fire drill.
Choose Internal vs. External Resources
Deciding who will conduct your IT audit is a critical step. You can use an internal audit team, hire an external firm, or use a combination of both. According to The Ohio Society of CPAs, organizations must apply sufficient resources and expertise to manage risks, whether they are internal or external.
Internal auditors offer deep knowledge of your company’s systems and culture. External auditors provide an objective, independent perspective and often have specialized skills for complex regulations. The best choice depends on your specific needs, the scope of the audit, and your in-house capabilities.
Create a Continuous Improvement Strategy
The goal of an IT audit is not just to pass but to improve. The findings should fuel a cycle of continuous improvement that strengthens your organization. This process depends on clear communication between auditors and your team to ensure everyone understands the objectives and results.
According to MSECB, this alignment helps manage scope creep and keeps the audit focused on key goals. After the audit, use the findings to refine controls, update documentation, and enhance security measures. As noted by Continuity Insights, IT auditors are key partners in this effort, helping to identify emerging threats and guide your organization toward better risk management.
Related Articles
IT Audit Process FAQs
Table of Contents

Mike Reeves, PhD
Mike is a key figure at the intersection of psychology and technology. He has created and managed algorithms and decision-making tools used by more than half of the Fortune 100.
